Simplify & Secure Your Online Life with Zeylink
Tired of Password Overload? Say goodbye to the endless cycle of forgotten, invalid, and insecure passwords for most of your online accounts. Zeylink drastically reduces your need for them, making your digital life simpler and more secure.
How it Works
Zeylink transforms your device into a secure identity anchor. By removing traditional passwords and PINs, it provides a seamless, cryptographic bridge between your app and any Zeylink-enabled service:
- Initiate: Click Login with Zeylink on the website. Depending on the site’s requirements, you may be asked to provide your email to match against your secure credentials.
- Scan: Open your Zeylink app and scan the unique QR code displayed on the screen to establish a secure handshake.
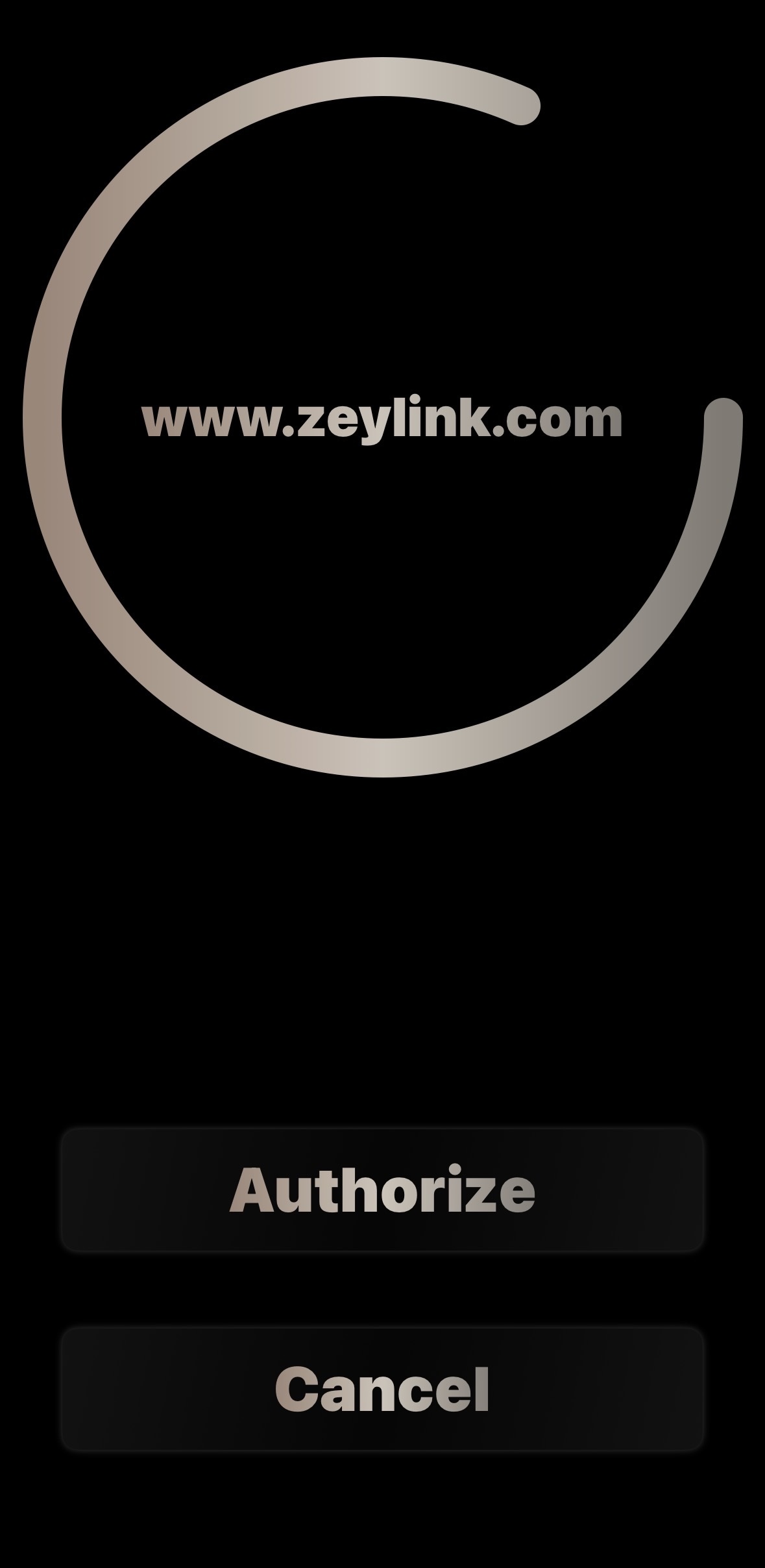
- Authorize: Perform a long-press on the Authorize button within the app. This intentional gesture signs the request using your device-bound private key.
- Finalize: Once authenticated, the website will either automatically poll the request or prompt you to click Continue to access your account.
Zeylink Benefits:
- You're in Charge: Zeylink isn't another company logging in for you. It's your personal keychain, giving you direct, secure access to your accounts on their websites. Your identity remains with the websites you trust.
- Significantly Fewer Passwords: Focus your strong, unique passwords only on crucial master accounts (like email).
- Isolate Security Breaches: Each Zeylink login creates a unique, site-specific credential. If a website you use ever suffers a breach, only that site is affected – your other accounts remain secure, unlike traditional password methods where one leak compromises many.
- Stronger Protection: Greatly enhance your security against common online threats like credential stuffing and data breaches.
- Phishing Resistant: Our unique login process makes phishing significantly more difficult compared to traditional password methods- there is no password to steal!
- Complete Privacy: We never collect or sell your data. Your information remains just that: truly yours.
At Zeylink, we believe your online experience should be effortless and inherently secure. By fundamentally rethinking how you access websites, we provide a solution that truly puts your privacy and protection first. Embrace a simpler, safer way to connect online.
Zeylink - Where Privacy meets Security.
Zeylink: The Future of Login.
Tired of password headaches, user churn, and the constant threat of account fraud?
Traditional authentication is broken. Users battle forgotten passwords, leading to frustration and support calls. Simultaneously, rampant password reuse and unauthorized account sharing pose significant security risks and drain revenue from your platform.
Zeylink fundamentally re-imagines user authentication. It eliminates traditional passwords entirely, offering a seamless, secure login experience that integrates directly with your existing user accounts.
How Zeylink Works for Your Users:
Zeylink establishes a secure, encrypted link between your website and the user's mobile device, where your website remains the ultimate authority for user identity:
- The Initial Request: The user clicks "Login with Zeylink" on your site. Your backend generates a unique session nonce and displays a QR code containing your API endpoint and the nonce. The user scans this with the Zeylink app.
- Verified Device Linking: For new devices or recovery, your website takes control of identity verification. You send a magic link or verification code to the user’s registered email. Once verified via your site's existing security (2FA, etc.), your site displays a secure QR code containing the unique 32-byte secret key.
- Secure Handshake & Key Rotation: Upon scanning the secret key, the app establishes a fully authenticated (AES-GCM) connection. From this point forward, the device and server utilize rotating cryptography to ensure Perfect Forward Secrecy.
- One-Tap Returning Login: For returning users, the process is effortless. The user scans the login QR code, authorizes the request on their device (via biometrics), and they are instantly logged in. No passwords, no PINs, and no friction.
Core Benefits for Your Platform:
- Eliminate Password Friction: Drastically reduce password reset requests, improving user satisfaction and cutting support costs for returning users.
- Unrivaled Security: Built on advanced, rotating cryptography. This neutralizes credential stuffing, brute-force attacks, and offline cracking.
- Combat Account Sharing & Fraud: Our unique single-device authentication ensures only the intended user can access their account, directly combating unauthorized sharing—critical for subscription-based models.
- Powerful Anti-Phishing: Traditional phishing relies on a remote attacker being miles (or oceans) away from the victim. Zeylink introduces a unique defense layer by providing websites with the IP addresses of both the device requesting the login (the desktop) and the device authorizing it (the phone).
- Dual-IP Correlation: Your platform can now verify that both devices are originating from the same network or geographic region in real-time.
- Virtual Geofencing: This allows for a "proximity-based" security model. If a login attempt occurs on a desktop in New York but is authorized by a phone in Eastern Europe, your backend can automatically flag or block the request as a high-risk phishing attempt.
- No GPS Required: Unlike traditional geofencing that requires invasive location permissions, Zeylink achieves this "Proximity Proof" using standard network metadata, maintaining user privacy while maximizing security.
- Zero-Knowledge Architecture: By eliminating static passwords, you drastically reduce the risk and "blast radius" of a potential data breach.
A Complementary & Powerful Integration
Zeylink isn't another Identity Provider (IdP) that takes control of your user data. Instead, it functions as a highly secure, personal digital keychain for your users' existing accounts on your platform.
- You Retain Control: Your website remains the central point of truth. Zeylink provides the secure "door," but your site holds the "ID check."
- Decentralized Security: Credentials are unique for each website and are never revealed to the user or stored in a central, hackable database.
- Developer First: Our core API is free to integrate. We provide robust documentation and PHP support files designed for easy, drop-in deployment.
Let's Build a More Secure Future, Together.
Zeylink is ready to redefine authentication, creating a safer and simpler web experience. We are actively seeking strategic partnerships with innovative platforms to embed our revolutionary authentication.
Eric Tiley, Founder
Support
Why is there no email required for setup?
Zeylink is designed as a 'Privacy-First' credential verifier. By not requiring an email, we ensure there is no central database to hack, no way to track your movements across the web, and no personal data to sell. We don't decide where you go; we just provide the keys.
How about cloud backup?
Cloud backup is an optional feature. If you choose to enable it, you will create a recovery account to store your encrypted keychain. This allows you to restore your access if your device is lost or stolen, though it does not support simultaneous use across multiple devices.
How do I log into more than one account on a site?
Currently there is no way to add additional logins for the same website. If there is a high demand for an option to have additional logins, then we can integrate that.
What is the 180-day expiration on keys?
To prevent 'stale' credentials from lingering on abandoned accounts, keys are valid for 180 days. You don't need to do anything special to renew them—simply logging into the site using the app automatically resets the timer for another 180 days.
How does the long-press authorization work?
To ensure security, Zeylink requires a deliberate long-press on the "Authorize" button. This prevents accidental logins and ensures that a cryptographic signature is only generated when you explicitly intend to access a site.
Why is my login being denied by a specific website?
Zeylink-enabled websites can set their own security policies. For example, a site may require that your device has an active Screen Lock (Passcode, FaceID, or TouchID) enabled. If your device does not meet the site’s security requirements, the app will notify you of a "Policy Violation" and the website will deny the handshake.
Why does my login always say expired?
The Zeylink login QR code is a time-sensitive security measure that remains active for only 30 seconds to protect your account against phishing and replay attacks. This validation process relies on Universal Epoch Time; therefore, if your login is consistently expiring, it usually indicates that your device clock is out of sync. To ensure a reliable connection, please verify that your device is connected to the internet and that your system settings are set to "Set Time Automatically" so your local time remains perfectly aligned with the global standard
Is a Screen Lock required to use Zeylink?
While the app functions without one, we strongly recommend having a system-level Screen Lock enabled. Your device is your identity anchor; a Screen Lock ensures that if your phone is physically compromised, your cryptographic keys remain protected by your device's hardware-level encryption.
How does Zeylink handle different login scenarios?
Zeylink identifies whether a request was initiated via a QR Scan or a Deep-Link to ensure the session context is correct. This allows websites to apply logical checks based on your device and the request. If the context is illogical, the website may deny the request.
My device is unable to sync with a website
If your device is unable to sync with a website, make sure to check those previous bullets. If it is still unable to sync with a website, you may need to contact that website for support. The Zeylink app just stores the login keys like a keychain. We have no access to the individual keys, or have any influence over them.
How do I remove a key?
To remove a key from your keychain, simply click Keychain from the main menu, select the key that you would like to remove, and then long press until prompted. Select Remove. This will remove the login credential from the website as well.
How do I remove my account from a device?
To remove your account, simply long press Keychain on the main menu until prompted. Select Remove, and the app will wipe all of its data and reset.
How do I handle a lost or stolen device?
Since Zeylink is decentralized, we cannot remotely disable your keys. We highly recommend utilizing your phone's built-in remote wipe features.
Deactivate Apple Device
Deactivate Android Device
I need assistance implementing the API
You can contact us at support@zeylink.com. Please allow us 24 to 48 hours to respond back to you.
Privacy Policy
Last Updated: April 2026
Zeylink ("we," "our," or "us") is committed to protecting your privacy. Our architecture is designed to minimize data collection, focusing on secure, decentralized authentication. This policy explains how we handle hardware permissions and ephemeral data.
1. Camera Access
Zeylink requires access to your device's Camera specifically to facilitate the scanning of QR codes for secure authentication.
- Scope of Use: The camera is used solely for local image processing to decode QR data.
- Storage & Sharing: We do not capture, record, or store any photos or videos. Processing is performed ephemerally on your device; no camera data is ever transmitted to our servers.
2. Biometric Authentication
Zeylink supports Biometric Authentication (such as fingerprint or facial recognition) as an optional security layer to verify your identity.
- Scope of Use: Zeylink utilizes standard system APIs (Android BiometricPrompt / iOS LocalAuthentication) to request verification.
- Storage & Sharing: Zeylink never accesses or stores your biometric data. All processing is handled by your device's secure hardware (Secure Enclave/TEE). We only receive a success or failure token from the operating system.
3. Website Cookies & Local Storage
To facilitate the "Hybrid" login archetype and maintain session integrity, we use secure, temporary session cookies. These are strictly necessary for functionality and are never used for cross-site tracking or advertising.
- Ephemeral by Design: These cookies are set with a "Zero-Lifetime" parameter, meaning they exist only in your browser's memory and are automatically purged the moment you close your tab or browser.
- Hardened Security: Our cookies are protected with HttpOnly and Strict SameSite flags. This prevents malicious scripts from accessing your session and ensures your authentication data is never transmitted to third-party websites.
4. Data Sovereignty & Storage
Zeylink acts as a decentralized authentication engine. We believe that your identity data should remain between you and the websites you trust.
- Decentralized Model: For third-party sites using the Zeylink API, Zeylink (the company) never receives, processes, or stores your login data. All authentication records are stored within the "Siloed" infrastructure of the specific website you are accessing.
- Showcase & Cloud Users: For users interacting with our official showcase or cloud-hosted instances, we only store the minimum necessary authentication stubs. These stubs contain no personal identifiers (like names or phone numbers) and are purged automatically after 180 days of inactivity.
- No Centralized Tracking: Because each Zeylink integration is an independent "black box," there is no central database that can track your movement across different websites.
5. Children’s Privacy
Zeylink does not knowingly collect personal information from children under the age of 13. While our mobile application operates anonymously and does not require personal details, our Web Showcase allows users to voluntarily enter an email address to demonstrate specific login archetypes.
Any email addresses provided for the showcase are stored solely to facilitate the demo and are not used for marketing or third-party tracking. If you believe a child under 13 has provided an email address through our showcase, please contact us at support@zeylink.com so we can immediately purge that data from our temporary records.
6. Data Control & Contact
Zeylink is designed with Data Minimization at its core. Most authentication records are composed of anonymized identifiers (UUIDs) and high-entropy random bytes, meaning they do not contain personally identifiable information (PII) in the traditional sense.
- User Control: You maintain absolute control over your digital footprint. To revoke access to a specific site, simply remove the linked account within your Zeylink mobile app. This immediately invalidates the cryptographic handshake.
- Anonymized Records: Our database primarily stores technical stubs (ID lookups and encrypted keys). We do not have the technical means to link these specific stubs back to your real-world identity.
- Manual Data Erasure: While showcase emails and inactive records are automatically purged after 180 days, you may request an earlier deletion of your showcase data at any time.
For any questions regarding our decentralized architecture or to request a data purge, please reach out to us at: Support@Zeylink.com
7. Updates to this Policy
Zeylink is an evolving project. We may update this Privacy Policy from time to time to reflect changes in our technology or legal requirements. Any changes will be posted directly on this page, and the "Last Updated" date at the top will be adjusted accordingly. We encourage you to review this page periodically to stay informed about how we are protecting your data.
Register Account
At this point, the website would typically email you your reset link. The link would link back to the website, using an unique ID linked to our account. The website may require additional 2FA or other verification, as they see fit.
For this demo, we will not email you a reset link, but instead directly display it below. This is not typically how a website will verify you. We are simply speeding up the process just to show you how it would be done.
Please click on the reset link below to be directed to a page that would be typical of what you might see.
Click Here